Banks and credit card companies charge high fees but part of those fees pays for security.
When fraud happens, they reverse transactions.
When passwords are lost, they reset them.
When accounts are compromised, they investigate.
Cryptocurrency works differently.
If you’re going to invest in crypto, you must understand one critical truth:
There is no bank.
There is no reset button.
There is only you.
In this guide, we’ll break down:
- Why crypto security matters more than ever
- The difference between hot and cold wallets
- What public and private keys really are
- The history of public-key cryptography
- Why losing your private key means losing your money forever
- How SHA-256 secures Bitcoin
- Why governments continuously attempt to break encryption
Let’s begin.
Why Cryptocurrency Security Is Different From Banks
Traditional financial institutions act as intermediaries. They protect your assets and charge you for it.
With cryptocurrency:
- There is no central authority protecting your funds.
- There is no fraud department.
- There is no “forgot password” option.
If your private key is compromised, your crypto can be stolen instantly and permanently.
If your private key is lost, your crypto is gone forever.
That’s why part of the money you save on banking fees should be reinvested into security tools like:
- Hardware wallets (cold storage)
- Secure software wallets (hot storage)
- Backup systems
- Password managers
- Encrypted storage devices
Crypto security isn’t optional. It’s foundational.
Hot Wallets vs Cold Wallets (Online vs Offline Storage)

When securing cryptocurrency, you’ll hear two key terms:
🔥 Hot Wallets
Connected to the internet.
Examples:
- Mobile apps
- Browser extensions
- Exchange wallets
Pros:
- Convenient
- Fast transactions
Cons:
- More vulnerable to hacking
❄️ Cold Wallets
Offline storage devices.
Examples:
- Hardware wallets
- Paper wallets
- Air-gapped systems
Pros:
- Much more secure
- Immune to online attacks
Cons:
- Less convenient
- Must be physically protected
The smart approach? Use both.
Store long-term holdings in cold storage.
Keep smaller trading balances in hot wallets.
The Two-Key System: Public and Private Keys Explained
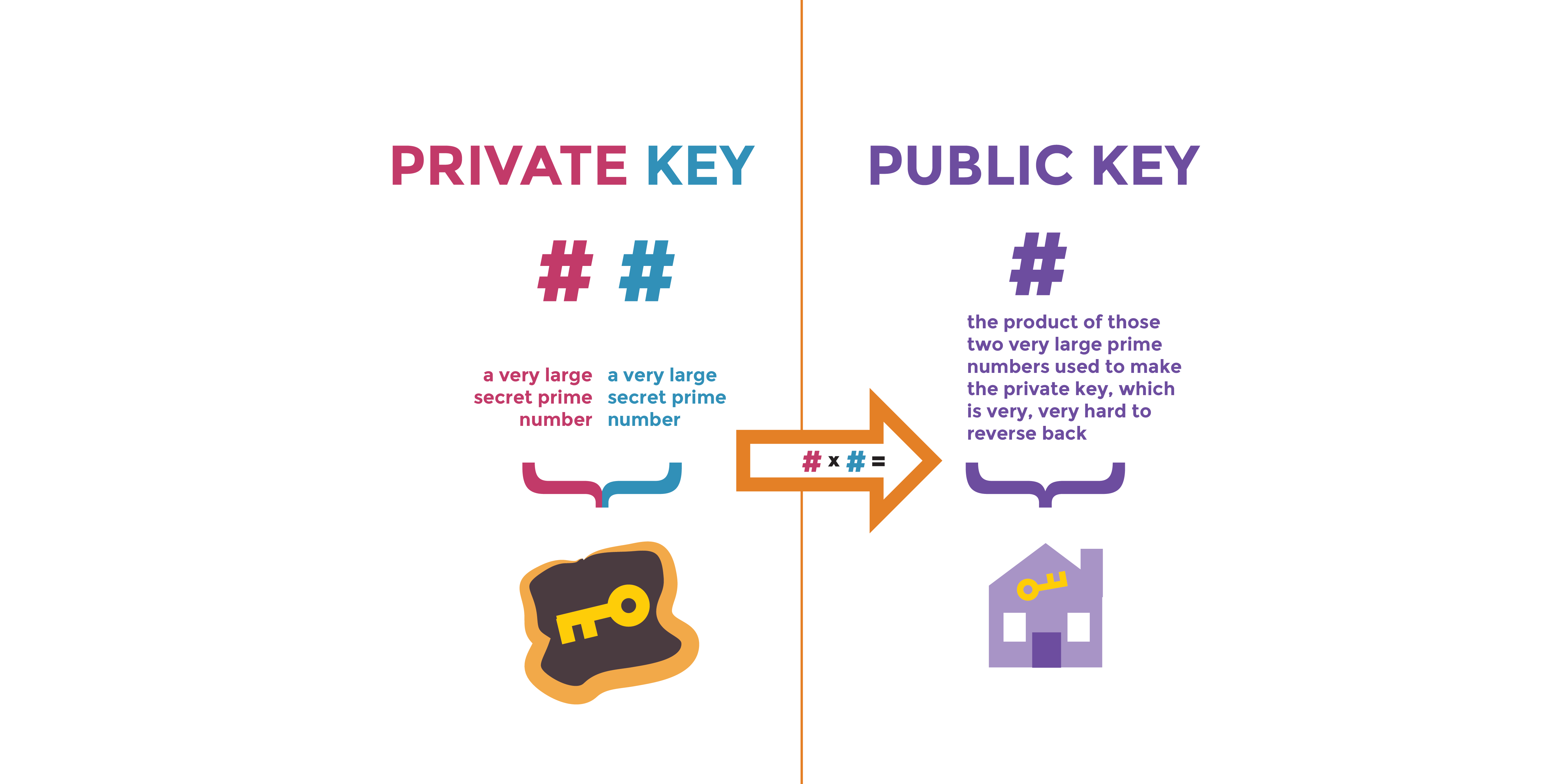
Cryptocurrency transactions rely on public-key cryptography, invented in 1976 by Stanford professor Martin Hellman.
This breakthrough changed digital security forever.
To understand it, imagine a nuclear submarine.
Launching missiles requires two keys:
- One held by the captain.
- One held by a government official.
Crypto works similarly.
You have:
- Public Key → Like your email address.
- Private Key → Like your email password.
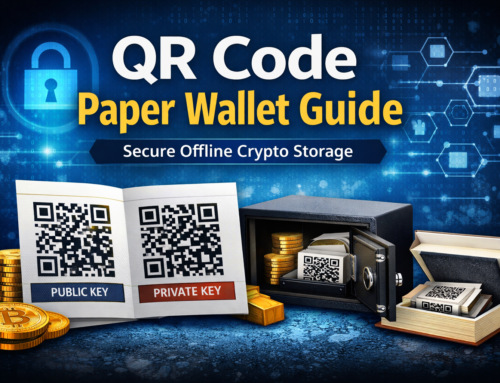
What Is a Public Key?
Your public key:
- Can be shared with anyone.
- Allows people to send cryptocurrency to you.
- Is often displayed as a QR code.
Think of it like a bank account number.
It’s safe to share.
What Is a Private Key?
Your private key:
- Must NEVER be shared.
- Unlocks access to your cryptocurrency.
- Proves ownership.
If someone gets your private key, they control your funds.
If you lose your private key, your crypto is permanently inaccessible.
Unlike Gmail, there is no password recovery.
Critical Rule
Your public key can NEVER reveal your private key.
But your private key can mathematically generate your public key.
This one-way relationship is what makes public-key cryptography secure.
The History of Modern Cryptography
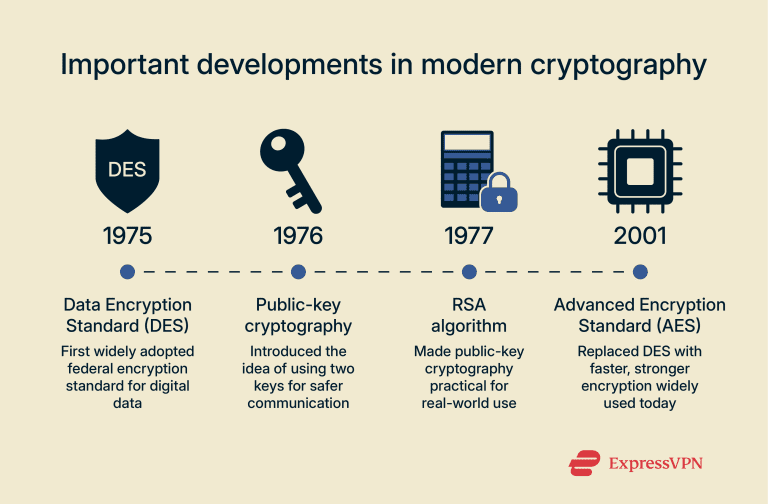
Understanding crypto security means understanding cryptography.
Public-key cryptography emerged during Cold War tensions between academic researchers and the National Security Agency.
Martin Hellman vs the NSA
When Hellman published his work, the NSA urged him to remain silent for national security reasons.
He refused.
This ethical debate shaped modern encryption.
RSA Encryption
After Hellman’s discovery, three mathematicians:
- Ron Rivest
- Adi Shamir
- Leonard Adleman
Developed the RSA cryptosystem.
RSA became foundational for internet security and authentication tokens worldwide.
Cryptography is math. Pure math.
Alan Turing and Codebreaking
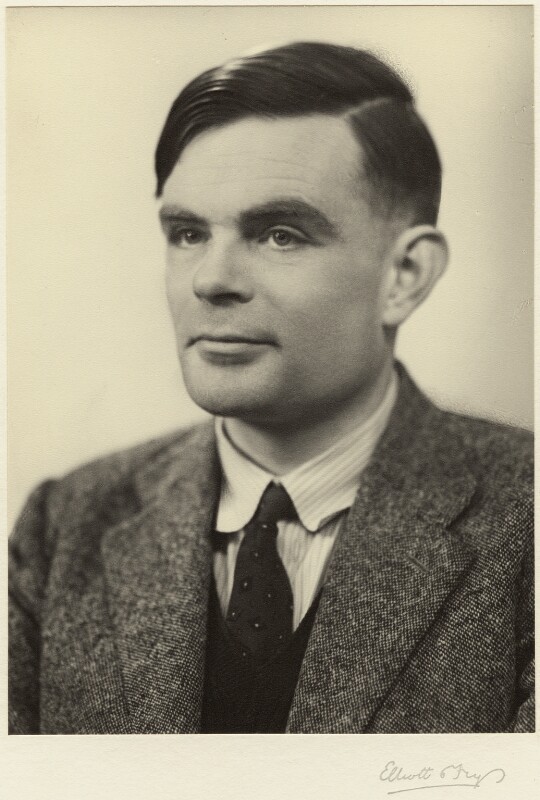

Long before cryptocurrency, Alan Turing and his team built machines to break Nazi encryption during World War II.
The Enigma machine was thought to be unbreakable.
It wasn’t.
Lesson:
No encryption is permanently secure.
Governments invest billions trying to break cryptographic systems.
And they will continue doing so.
SHA-1 vs SHA-256: The Hash Algorithms Behind Bitcoin
Cryptocurrency relies on secure hashing algorithms.
Two important ones:
- SHA-1 (Secure Hash Algorithm 1)
- SHA-256 (used by Bitcoin)
SHA-256 was developed by the NSA in 2001 and is the backbone of Bitcoin’s security.
When you check Bitcoin market data on finance sites, you’ll see:
Algorithm: SHA-256
This algorithm secures:
- Transaction verification
- Mining
- Blockchain integrity
What Is a 51% Attack?
To compromise Bitcoin’s blockchain, an attacker would need to control over 50% of the global mining hash power.
That’s called a 51% attack.
For Bitcoin, this would require enormous computing power bordering on impossible at global scale.
This is why Bitcoin remains secure.
Governments, Cloud Security, and Crypto
Many governments distrust foreign cloud providers.
Security concerns drive what’s known as “cloud Balkanization” different countries building separate cloud ecosystems.
Why?
Because encryption backdoors and surveillance concerns exist.
If governments fight over encryption in cloud services, imagine how they view decentralized cryptocurrencies.
Cryptocurrency represents:
- Financial sovereignty
- Reduced government oversight
- Decentralized control
And that makes security a geopolitical issue.
The Human Responsibility of Crypto Ownership
With traditional banking:
- If your card is stolen, you call the bank.
- If your account is hacked, they reimburse you.
With crypto:
- If your private key is exposed, funds are gone.
- If you forget your seed phrase, funds are gone.
There is no customer support.
This is why education comes before investing.
Before buying Bitcoin, Ethereum, or any altcoin, you must understand:
- Wallet types
- Key management
- Backup procedures
- Encryption fundamentals
Final Thoughts: Security Before Speculation
Half of the word “cryptocurrency” is crypto meaning hidden or secret.
Security is not optional.
It’s the foundation.
If you don’t stay updated on:
- Cryptographic advances
- Security vulnerabilities
- Hardware wallet best practices
- Hashing algorithms
Then your money and privacy can be compromised.
Cybercriminals follow the money.
And there is a lot of money in crypto.
Protect it accordingly.




Leave A Comment