Encryption is the foundation of cryptocurrency security.
If you don’t understand how hashing and encryption work, you’re trusting your digital assets to something you don’t fully comprehend.
And in crypto, there are no banks to call. No chargebacks. No safety net.
In this guide, we’ll break down:
- How general encryption works
- What SHA-1 and SHA-256 are
- Why weak passwords get cracked
- Why SHA-1 is obsolete
- Why SHA-256 powers Bitcoin
- And what this means for protecting your crypto
Let’s simplify it.
What Is Encryption in Cryptocurrency?
At its core, encryption transforms readable data (like a password) into a fixed-length string of characters called a hash.
For example:
hello worldBecomes something like:
2aae6c35c94fcfb415dbe95f408b9ce91ee846edThat long string is the hash output.
This process is called hashing.
Unlike traditional encryption, hashing is designed to be one-way:
- You can easily generate a hash from text.
- But you shouldn’t be able to reverse it back to the original text.
In theory.
What Is SHA-1?
SHA-1 (Secure Hash Algorithm 1) was once a widely used cryptographic hash function.
Key characteristics:
- Produces a 40-character hash
- Developed in the 1990s
- Once used in SSL certificates
- Now considered insecure
Why SHA-1 Is Weak
When you hash simple inputs like:
hello worldpasswordpassword1234
They can be cracked easily.
Why?
Because attackers use:
- Precomputed hash databases
- Massive wordlists
- Dictionary attacks
- Brute-force computing
If your password is common, it has likely already been hashed and stored in a database somewhere.
That’s why simple passwords get “decrypted.”
Technically, they aren’t reversed, they’re matched against known hashes.
And that’s a huge difference.
Small Changes = Completely Different Hash
Here’s something powerful:
Add a space after hello world.
The entire 40-character output changes.
Change one letter to uppercase?
Completely different hash.
Hash functions are extremely sensitive to even tiny input changes.
This property is called the avalanche effect.
That’s what makes hashing powerful.
But strength depends on:
- The complexity of your input
- The strength of the hashing algorithm
Why SHA-1 Was Phased Out
By 2005, researchers began proving SHA-1 was vulnerable to collision attacks.
In 2017, companies like:
- Microsoft
- Apple
- Mozilla
Officially stopped allowing SHA-1 SSL certificates.
If the biggest tech companies in the world abandon a protocol, pay attention.
SHA-1 became obsolete.
Enter SHA-256: Stronger Hashing

In 2001, the NSA introduced SHA-2.
A variation of SHA-2 is SHA-256.
Key characteristics:
- Produces a 64-character hash
- Far stronger than SHA-1
- Requires significantly more computing power to crack
- Used by Bitcoin
And this is critical.
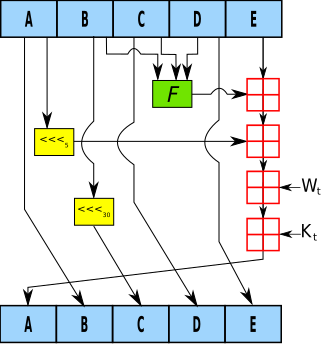
Why Bitcoin Uses SHA-256
Bitcoin uses SHA-256 in its mining process.
Every time Bitcoin miners compete to validate transactions:
- They hash block data
- They adjust a number called a nonce
- They attempt trillions of hashes per second
- They search for a hash that meets strict difficulty requirements
This is proof-of-work.
The security of Bitcoin depends on:
- The strength of SHA-256
- Massive global computing power
- The economic cost of attacking the network
If SHA-256 were ever broken, confidence in Bitcoin would collapse.
That’s why understanding hashing matters as an investor.
Can SHA-256 Be Cracked?
Yes.
Given:
- Enough computing power
- Enough time
- Weak enough inputs
All encryption can theoretically be broken.
Security is about practical impossibility, not theoretical impossibility.
Even SHA-256 hashes can be cracked if the original input is simple like:
passwordpassword1234admin
The algorithm may be strong.
But weak inputs destroy security.
The Real Lesson: Think Like a Hacker

To protect crypto, you must think like an attacker.
Ask:
- What would I try first?
- What passwords are common?
- What shortcuts do users take?
Most hacks succeed because of:
- Weak passwords
- Reused credentials
- Poor operational security
- Social engineering
Not because SHA-256 failed.
What This Means for Cryptocurrency Investors
If you’re investing in crypto, you must evaluate:
- What encryption algorithm does the blockchain use?
- Is it outdated?
- Has it been audited?
- Is it quantum-resistant?
- What happens if it gets compromised?
Security failures crush token prices.
Investor confidence disappears instantly.
SHA-1 vs SHA-256: Quick Comparison
| Feature | SHA-1 | SHA-256 |
|---|---|---|
| Hash Length | 40 characters | 64 characters |
| Year Released | 1995 | 2001 |
| Security Status | Deprecated | Still widely used |
| Used in Bitcoin? | No | Yes |
| Practical Strength | Weak | Stronger |
The Bigger Picture
When you learn how hashing works, you realize something powerful:
Security isn’t magic.
It’s math.
And math can be attacked with computing power.
That’s why:
- Protocol design matters
- Network size matters
- Mining difficulty matters
- Cryptographic evolution matters
If you’re serious about cryptocurrency, you must understand the security layer.
Because crypto removes banks.
Which means you are the bank.
And if you don’t understand how the lock works…
You’re trusting your wealth to something you don’t fully control.
Final Takeaway
- SHA-1 is outdated and insecure.
- SHA-256 is stronger and powers Bitcoin.
- Weak passwords break strong encryption.
- All locks can eventually be broken.
- Security requires staying ahead of attackers.
In crypto, ignorance is risk.
And security is not optional.
It’s survival.





Leave A Comment