Encryption is the foundation of cryptocurrency security.
If you don’t understand how hashing and encryption work, you’re essentially trusting your digital wealth to something you can’t evaluate.
And in crypto, there are no banks. No customer support hotline. No chargebacks.
In this guide, we’ll break down:
- How general encryption works
- Why simple passwords get cracked
- What SHA-1 is (and why it’s obsolete)
- Why SHA-256 is stronger
- How this connects to Bitcoin mining
- Why computing power changes everything
Let’s start simple.
What Is Encryption (In Simple Terms)?
Encryption transforms readable data into an unreadable format using a mathematical algorithm.
In cryptocurrency, we don’t just use encryption, we use cryptographic hashing.
Hashing takes an input (like a password or message) and converts it into a fixed-length string of characters.
For example:
Input:hello world
Output (SHA-1 hash):2aae6c35c94fcfb415dbe95f408b9ce91ee846ed
That 40-character string is the hash.
Change even ONE character like even a single space and the output becomes completely different.
This is called the avalanche effect.
Thinking Like a Hacker: Why Simple Passwords Fail

To understand crypto security, you must think like an attacker.
If you hash:
hello worldpasswordpassword1234
These are common phrases. Hackers already have databases containing millions, even billions, of commonly used passwords and their hashed equivalents.
When you try to “decrypt” a hash, you’re not reversing it mathematically. Instead, attackers:
- Take known words
- Hash them
- Compare results
- Repeat billions of times
If your password is simple, it gets cracked.
This is called a dictionary attack or brute force attack.
That’s why simplistic hashes were easily decrypted in your exercise.
SHA-1: Once Secure, Now Obsolete

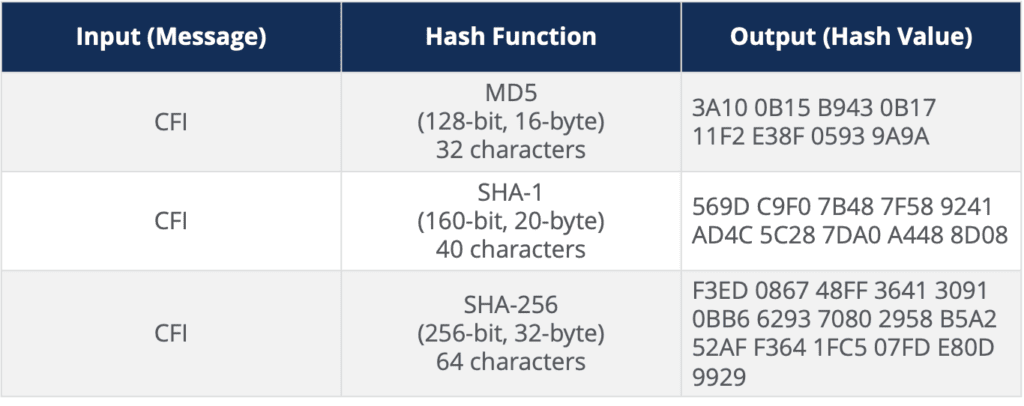
SHA-1 (Secure Hash Algorithm 1) was introduced in 1995.
It generates a:
- 40-character hash
- 160-bit output
For years, it was widely used in:
- SSL certificates
- Digital signatures
- Government systems (unclassified)
But by 2005, security experts realized SHA-1 was no longer strong enough.
In 2017, major companies like:
- Microsoft
- Apple
- Mozilla
Officially stopped accepting SHA-1 SSL certificates.
Why?
Because collisions and vulnerabilities were discovered.
And in cybersecurity, once cracks appear, confidence collapses.
SHA-256: Stronger, Longer, More Secure
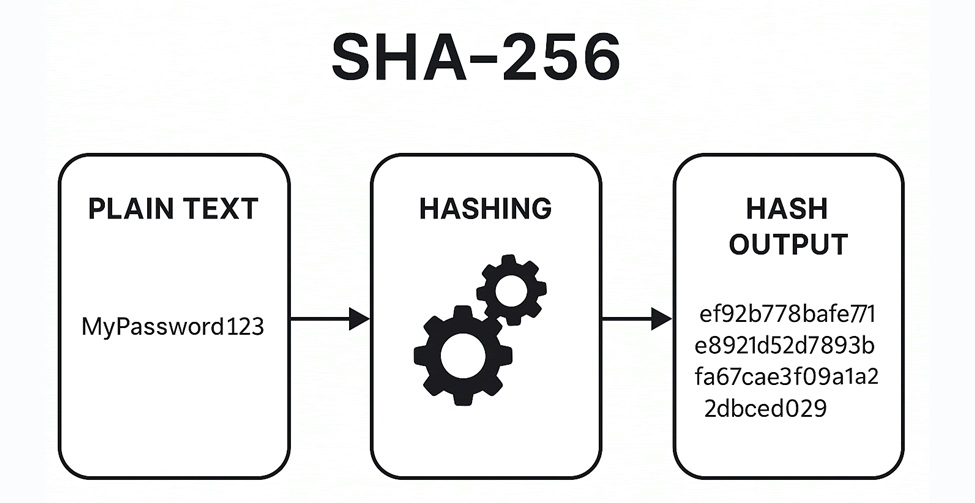
In 2001, the NSA introduced SHA-2.
A popular version of SHA-2 is SHA-256.
It generates:
- A 64-character hash
- 256-bit output
Example:
Input:password1234
SHA-1 Output:
40 characters
SHA-256 Output:
64 characters
Longer hash = exponentially more possible combinations.
More combinations = dramatically harder to brute force.
But here’s the key:
Stronger does not mean unbreakable.
It only means:
- It requires significantly more computing power
- It takes longer
- It’s currently economically impractical to break at scale
Why Bitcoin Uses SHA-256
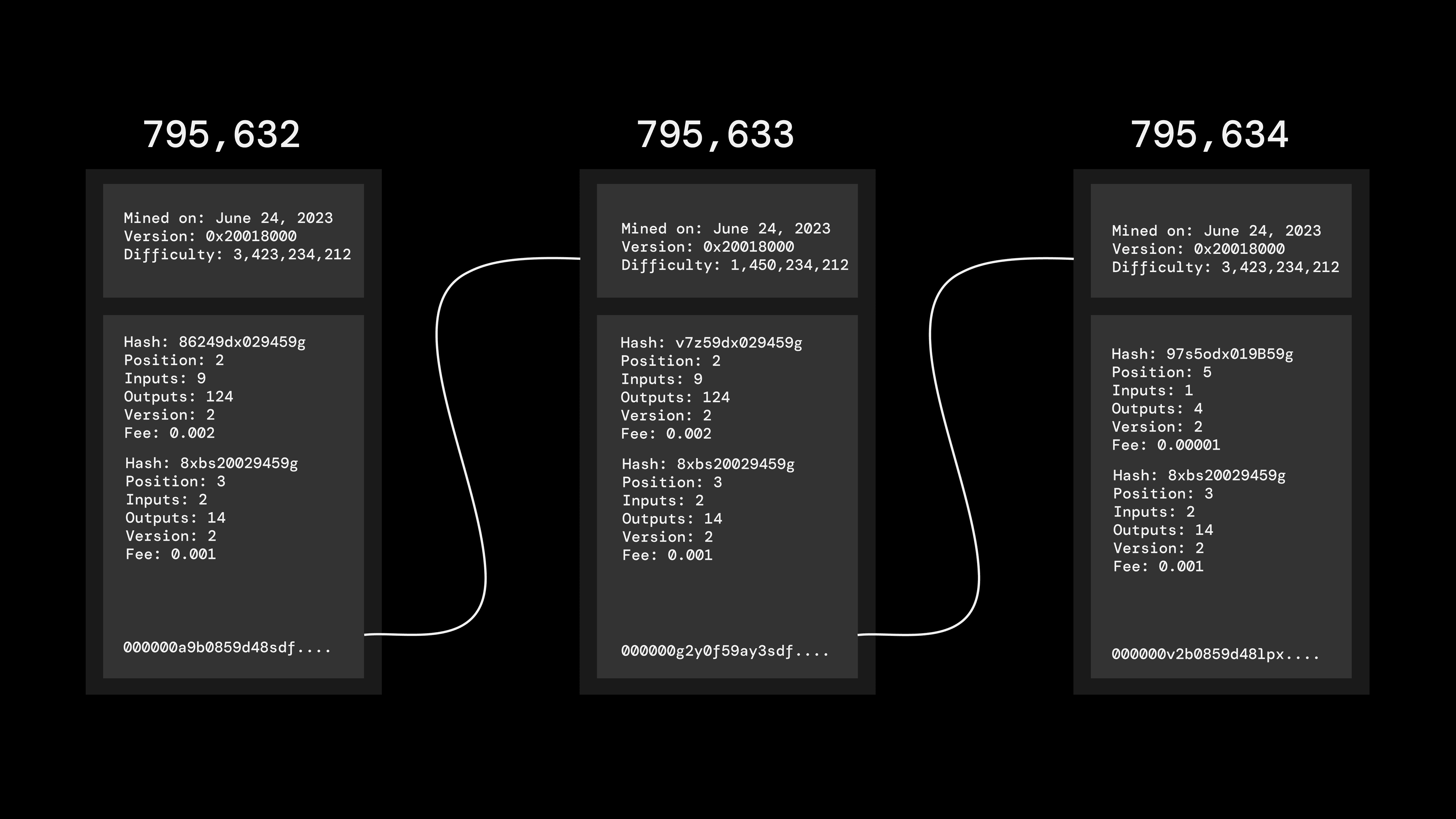
Bitcoin uses SHA-256 hashing for:
- Block validation
- Mining
- Transaction security
When miners compete to validate blocks, they are:
- Generating hashes
- Attempting trillions of combinations per second
- Competing to find a valid hash under network difficulty
This is called Proof of Work.
Mining is essentially:
A global brute-force hashing competition powered by massive computing infrastructure.
That’s why understanding hashing matters.
If SHA-256 were ever compromised at scale, Bitcoin’s security, and price, would collapse.
Security confidence drives valuation.
The Hard Truth: All Codes Can Be Broken
Given:
- Enough computing power
- Enough time
- Enough financial incentive
Any cryptographic system can eventually be compromised.
History proves this.
Old bike locks were considered secure… until someone figured out how to open them with pen caps.
Security is always:
A race between encryption strength and computing power.
That’s why SHA-1 was phased out.
And one day, even SHA-256 may be replaced.
Quantum computing could accelerate this timeline.
Why This Matters for Crypto Investors
If you invest in cryptocurrency, you must evaluate:
- What hashing algorithm it uses
- Whether it has known vulnerabilities
- If its encryption has been audited
- How resistant it is to brute-force attacks
If a project’s underlying cryptography fails, the token price will follow.
Security isn’t optional.
It’s foundational.
Key Takeaways
- Hashing converts input into fixed-length output.
- SHA-1 produces 40-character hashes and is obsolete.
- SHA-256 produces 64-character hashes and is stronger.
- Simple passwords get cracked easily via dictionary attacks.
- Bitcoin mining uses SHA-256.
- All encryption can eventually be broken, computing power is the variable.
Final Thought
Cryptocurrency removes banks from the equation.
Which means:
You are your own security department.
The moment you understand hashing, password complexity, and brute-force logic, you’ll never use weak passwords again.
And that’s the first step toward protecting digital wealth.



Leave A Comment