Cryptocurrency gives you full control over your money.
But with control comes responsibility.
In this lesson, we’re diving deep into crypto security fundamentals the concepts that protect your digital assets from hacks, theft, and irreversible loss.
If you’re serious about cryptocurrency investing or trading, understanding security isn’t optional. It’s foundational.
Why Crypto Security Matters More Than Ever
Unlike traditional finance, cryptocurrency operates in a decentralized environment.
There are:
- No banks to reverse fraudulent transactions
- No credit card chargebacks
- No customer support hotline that can restore stolen funds
If your wallet is compromised, your crypto is likely gone permanently.
That’s why cryptography, the science of secure communication is the cornerstone of cryptocurrency.
Every major blockchain system depends on cryptographic algorithms to:
- Verify transactions
- Secure private keys
- Prevent double spending
- Maintain network integrity
Understanding how these mechanisms work gives you an enormous edge as an investor or trader.
What Is a Cryptocurrency Wallet?

A cryptocurrency wallet doesn’t actually store your coins.
Instead, it stores your private keys, which give you access to funds recorded on the blockchain.
Think of it this way:
- The blockchain is the ledger.
- Your wallet holds the credentials that prove ownership.
There are different types of wallets, including:
- Software wallets
- Hardware wallets
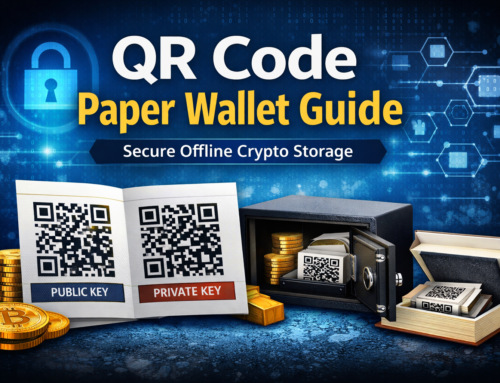
- Paper wallets
- Mobile wallets
- Exchange wallets
Each has its own security trade-offs.
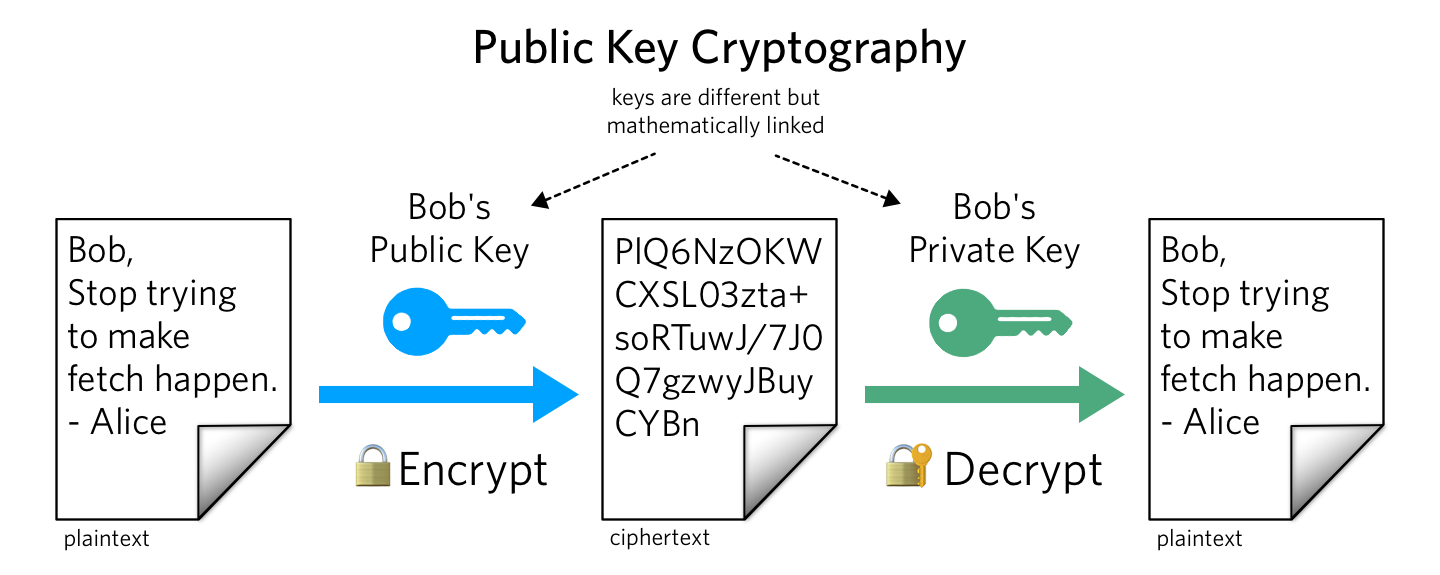
Public Keys vs Private Keys (Simple Explanation)

Understanding public and private keys is critical.
Private Key
- A secret string of numbers and letters.
- Grants full access to your cryptocurrency.
- Must never be shared.
- Whoever controls the private key controls the funds.
Public Key
- Derived mathematically from the private key.
- Can be shared safely.
- Used to receive cryptocurrency.
- Generates your wallet address.
In simple terms:
Your public key is like your email address.
Your private key is like your password but far more important.
Lose your private key?
You lose access permanently.
What Is Hashing?
Hashing is a cryptographic process that converts input data into a fixed-length string.
No matter how long the original input is, the output will always be the same length.
Key properties of hashing:
- One-way function (cannot reverse it)
- Deterministic (same input = same output)
- Highly sensitive to change (tiny input change = completely different hash)
Hashing secures blockchains by:
- Protecting transaction data
- Securing wallet addresses
- Enabling mining validation
SHA-1 vs SHA-256: What’s the Difference?
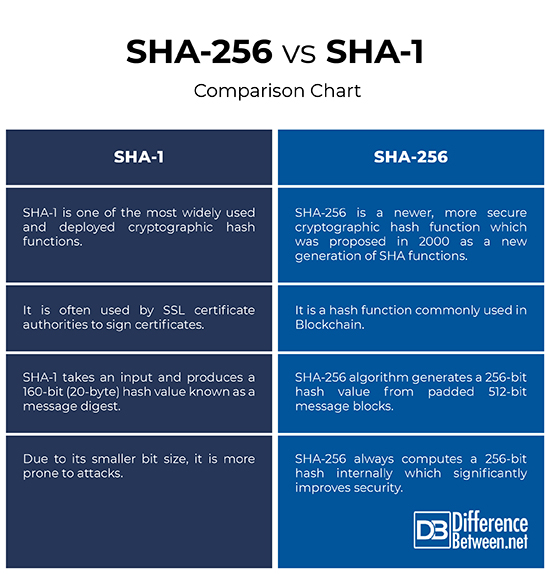
SHA-1 (Secure Hash Algorithm 1)
- Older hashing algorithm
- Produces 160-bit output
- No longer considered secure
- Vulnerable to collision attacks
SHA-256 (Secure Hash Algorithm 256)
- Produces 256-bit output
- Much stronger cryptographic security
- Extremely resistant to brute force attacks
- Used in major cryptocurrencies like Bitcoin
SHA-256 is one of the core cryptographic algorithms that powers Bitcoin’s security model.
When people say “Bitcoin is secure,” they are largely referring to the strength of SHA-256 hashing combined with decentralized consensus.
Cold Storage vs Hot Storage

Understanding storage types is essential for protecting your crypto capital.
Hot Storage
- Connected to the internet
- Convenient
- Faster transactions
- Higher hack risk
Examples:
- Exchange wallets
- Mobile wallets
- Browser wallets
Cold Storage
- Offline storage
- Much more secure
- Immune to online hacks
- Ideal for long-term holdings
Examples:
- Hardware wallets
- Paper wallets
- Air-gapped devices
For serious investors, a hybrid approach often works best:
- Small amount in hot storage
- Majority in cold storage
Security is about reducing attack surfaces.
Practical Exercise: Encrypting & Decrypting Data
Theory is useful.
Practice builds mastery.
After learning about SHA-1 and SHA-256, you’ll:
- Encrypt text using weaker protocols (SHA-1)
- Compare outputs
- See why SHA-256 is far superior
- Understand how blockchain hashing protects data
This hands-on approach makes abstract cryptography tangible.
Why Security Comes First in Crypto Education
Many beginners rush straight into:
- Trading strategies
- Altcoin speculation
- DeFi platforms
- Meme tokens
But without security knowledge, profits can disappear overnight.
Security is not optional.
It’s the foundation.
In cryptocurrency, you are your own bank.
That’s empowering, but only if you understand how to protect yourself.
Final Thoughts
In this first security-focused module, you’ve learned:
- How crypto wallets work
- The importance of private keys
- What hashing is
- Why SHA-256 matters
- The difference between hot and cold storage
- How to create a paper wallet
These concepts are the bedrock of cryptocurrency security.
Master them now and you’ll avoid catastrophic mistakes later.
Before you move forward in your crypto journey, make sure your foundation is strong.
Because in crypto, security isn’t a feature.
It’s survival.




Leave A Comment